The Instructure Canvas Breach

The Instructure Canvas Breach: A Technical and Strategic Breakdown of One of Education’s Largest Cybersecurity Incidents On April 30, 2026, Instructure, the company behind the Canvas learning management system, disclosed a major cybersecurity incident involving unauthorized access to internal systems and the theft of sensitive platform data. Within days, the threat actor known as ShinyHunters […]
Two breaches, one lesson

Two breaches, one lesson: AI trust is the new attack surface In April 2026, a single compromised OAuth token and a single misconfigured database policy exposed two of the most influential platforms in modern web development. Vercel — the Next.js creator valued at $9.3 billion — disclosed on April 19, 2026 that attackers pivoted from […]
How Hackers Can Hijack AI Agents Through Malicious Web Content
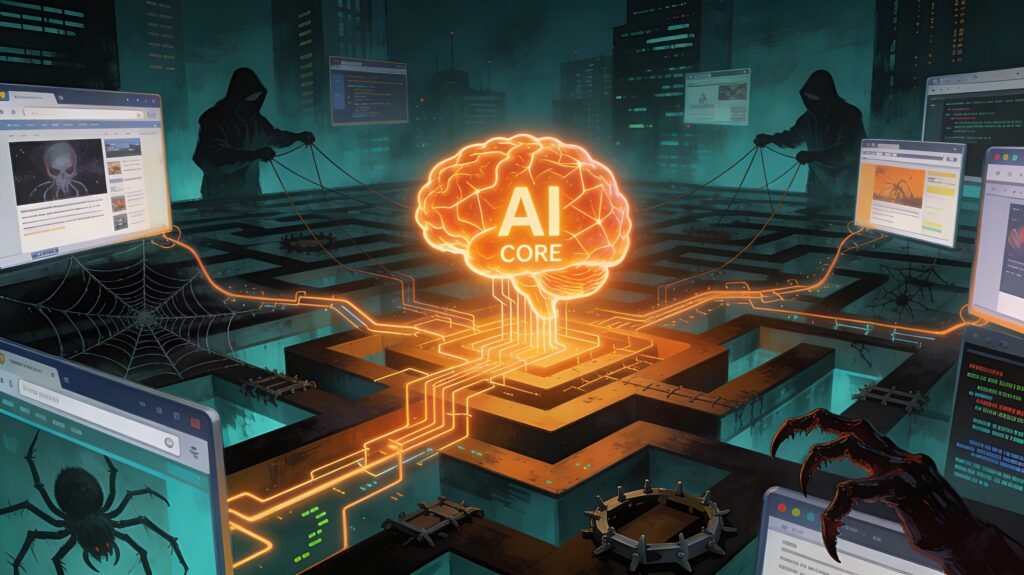
How Hackers Can Hijack AI Agents Through Malicious Web Content AI agents are everywhere now. They browse websites, manage emails, execute financial transactions, and call external APIs without human input. That autonomy is the point. It is also the problem. In late March 2026, Google DeepMind published a research paper called “AI Agent Traps.” It […]
Vibe Coding: A Security Crisis Hidden Behind the Hype

Vibe Coding: A Security Crisis Hidden Behind the Hype What Is Vibe Coding? AI researcher Andrej Karpathy coined the term in February 2025. Collins Dictionary named it Word of the Year that same year. The idea: you describe what you want to build in plain English, an AI model like Claude, GPT-4o, or a tool […]
Hackers Gone Wild: The Biggest Cyber Incidents of 2026 (So Far)

Hackers Gone Wild: The Biggest Cyber Incidents of 2026 (So Far) We are barely three months into 2026 and hackers are already making this one of the most dangerous years in cybersecurity history. From Iran-linked wiper attacks erasing 200,000 devices overnight to a ransomware gang shutting down a hospital for nine days, the digital battlefield […]
Project TajMahal: The Ghost in the Machine

Project TajMahal: The Ghost in the Machine What Happened In the fall of 2018, researchers at Kaspersky Lab found something they had never seen before. Buried inside a diplomatic network was a fully operational cyber-espionage framework. It was complex, well-engineered, and had been sitting there quietly for at least five years. They named it Project […]
The Invisible Mercenaries

The Invisible Mercenaries: How Anonymous Cyber Hit Men Built a Shadow Industry Law Enforcement Still Cannot Dismantle In 2017, a federal courtroom in Minneapolis revealed one of the most uncomfortable truths in modern cybercrime. A defense attorney, arguing for her client, a man who hired hackers to attack dozens of websites, pointed out something that […]
The WANK Worm

The WANK Worm: When Someone Hacked NASA and Got Away With It This is the first story in a series about hackers who pulled off major attacks and were never caught. These are the ghosts in the machine. The ones who walked away clean. October 1989: The Perfect Storm The Berlin Wall was about to […]
The Ghost With a Grudge

The Ghost With a Grudge: How the Impact Team Destroyed Ashley Madison and Vanished July 12, 2015. Employees at Ashley Madison powered on their computers. AC/DC’s “Thunderstruck” blasted from their speakers. A ransom message filled their screens. The Impact Team had arrived. Their demand was simple. Shut down Ashley Madison and Established Men within 30 […]
The Max Headroom Signal Hijacking

The Max Headroom Signal Hijacking: Television’s Greatest Unsolved Hack On November 22, 1987, thousands of Chicago television viewers watched something they’d never seen before. A bizarre masked figure invaded their screens twice in one night. The hijacker took over two major TV stations in what remains one of the most audacious and mysterious hacks in […]
